Just got back from the USA where we delivered some HTC D4 Secure phones to customers and showed them how to set them up. We didn’t have to show them how to use them because it’s actually hard to tell you’re using a non-stock Android phone. They all seemed interested and initially happy with the product and now we’re eagerly awaiting their feedback and questions. It’s exciting to see our products leave the development cradle and hit the hands of actual users in the real world!
The phones we’re shipping right now have got three main virtual machines running on the OKL4 Microvisor: Android, DIT (Data In Transit), and Block Storage.
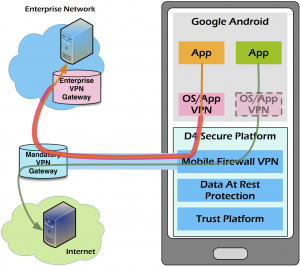
The DIT VM is a Linux box with a Strongswan VPN client, and can also perform network traffic filtering and auditing. All network traffic from Android must pass through the DIT VM, so that means every app running on Android is now transparently communicating through a VPN tunnel back to a secure server. If you want, you can also run a VPN-client app in Android, so that means you will have double layer VPN which is very cool and very secure.
The Block VM is another Linux box that controls the SD card and eMMC (flash memory) hardware peripherals of the phone, so all data being read or written to storage must pass through it. That means we can implement another level of access controls to disk partitions. Android already has Full Disk Encryption permanently enabled on the data partition, and in a forthcoming firmware update we will have an optional second layer of disk encryption implemented that is always on too. This second layer of disk encryption for Data At Rest (DAR) along with nested VPN will mean the phone lives up to it’s promise: D4 = Double DIT, Double DAR!
If you’re interested in learning more, check it out here.
