Mobile
Embedding the Aegis Secure solution in a mobile device provides an unparalleled level of data and system security. The architecture leverages Type 1 Virtualization to split the mobile device functions into multiple virtual machines (VMs) to allow for greater operational integrity, more granular system control, and a reduced attack surface. Various rules of operation govern the interactions across functional areas and between virtual machines. These rules ensure that the system functions in very specific ways.
The HTC A9, Secured By D4, is the initial first generation reference device for Ultra-Secure mobile solution and includes the following features: Boot integrity validation, isolated DIT (VPN), isolated and controlled storage (eMMC), isolated userland (Android OS), and isolated cryptographic functions (Entropy and Key Store). D4 Secure is configured in such a way that communications to and from the device must traverse a VPN. This allows for sensitive areas like Entropy and Key Store to be protected from potentially high-risk areas such as the Android OS. The most current example is our second generation solution leveraging the Aegis Secure platform and now deployed on a mobile device is the Aegis A51 Ultra-Secure Mobile Device.
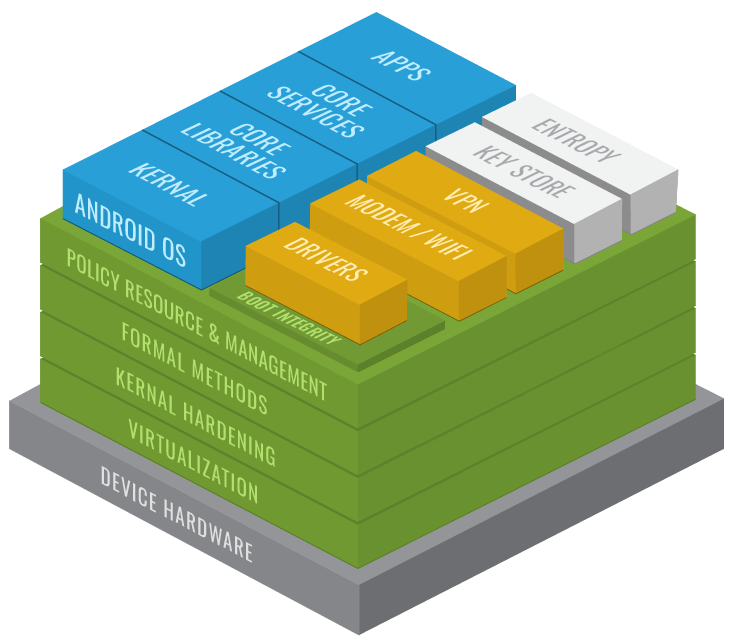
Aegis Secure SDK –The virtualization technology and framework that allows for the creation, configuration, and execution of the various function areas and virtual machines of a system.
Cog Secure Boot — Validates and verifies which configurations and systems are to be booted and loaded onto a device.
HW Platform –device on which the Aegis Secure platform is installed. It consists of the CPU / SoC and embedded components that make up a device.
Functional Areas
- Android OS –This VM contains the Android OS including most of the general-purpose device drivers. It provides standard functions of the device from the end user’s perspective.
- Entropy –This VM is responsible for pseudo random number generation for various cryptographic functions of the system. The reliable generation of cryptographically sound random numbers is vital to the system security and integrity.
- Key Store–Cryptographic keys for encrypted areas of the system are controlled in this VM. Having these keys isolated from the rest of the system is critical for system-wide assurance.
- Secure DIT –The DIT (Data in Transit) VM processes all of the data streams that traverse the Modem and WiFi areas. It encrypts this data and sends it across a VPN; protecting the data against eavesdropping and other attacks.
- Secure DAR –The DAR (Data at Rest) VM provides encrypted filesystem support for the various parts of the system. This ensures that data stored on the device is not accessible by unauthorized parties.
- Modem / WiFi –This VM (within Android in the D4 Secure Base Reference Architecture) is where the data streams that flow across the device’s cellular modem or 802.11 wireless device are managed. By managing these flows of data, more granular control over the data is achieved.
- Block –This VM controls the data streams that flow in or out of the device’s eMMC (physical storage). The isolation of storage functionality allows for highly managed control of data being stored on the device.
The practical applications of the solution unlock the potential of your mobile device, while gaining defense-in-depth security. US Government NIAP Certification complete for CSfC, including the MDF, VPN, and FDE Protection Profiles.
