Our Modular Approach
Be sure with Ultra-Secure Mobility™ Products
With over five years of experience developing Ultra-Secure Mobile devices for select Western Governments, Aegis has solved the riddle of marrying the commercial market to the needs of the Ultra-Secure Mobility™ customer. The answer was always there, but the execution was the tricky bit. To that end, Aegis Secure is offering Ultra-Secure Mobility products for the market by combining technology to bring the first true set of commercial Ultra-Secure Mobility products. The definition for Ultra-Secure Mobility™ can be illustrated by a solution that delivers a combination of all the following:
● High assurance, Certified security
● End-User defined privacy
● Assured through Formally Proven virtualization
● Top-notch user experience
Aegis Ultra-Secure Mobility™ devices offer defense-in-depth resilience with an architecture that is layered, isolated, and modular – built on top of a hardened Hardware platform, a formally verified Type-1 hypervisor the uses virtualization to separate drivers and user environments, the flexibility to control your policies, non bypassable network and data protections to build Government and Enterprise grade products.
Modularity Drives to Zero Trust
Using type-1 virtualization embodies a fundamental innovation in the delivery of OS functionality: modularity. With a virtualized OS, the hypervisor works with a team of optional cooperating processes that provide higher-level OS functionality. Critically, unlike with a monolithic kernel, these processes run in user space; that is, outside privileged kernel space.
A virtualized architecture is based on the concept of least privilege. Only the kernel is granted access to the entire system. A virtualization tool like the Bedrock Systems Virtualization encapsulates each application and OS service in its own isolated process space. The microkernel protects and allocates memory, and gives drivers and other OS services only the minimum privileges they need to perform their functions. This is when it leads to us to the ultimate goal of Zero Trust.
Fault containment through isolation and least privilege prevents errors and exploits from affecting other parts of the system. The only thing a component can crash is itself. Such crashes can be easily detected, and, since the virtualization layer is unaffected, the faulty component can be restarted while the system is running with minimal impact on performance. In short, in the event of a kernel crash in a monolithic kernel system the only response is to reboot the system, while with a virtualized system it can usually repair itself to provide a much better mean time between failures (MTBF).
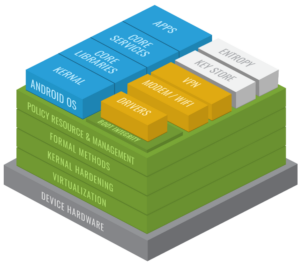
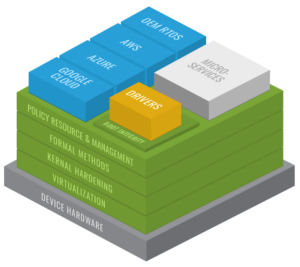
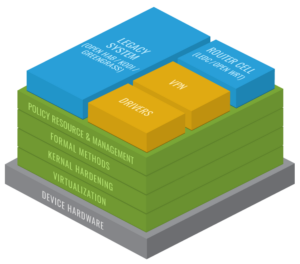
Here is an example of an architectural approach for a modularly designed system:
Secure Mobile
Edge Compute
Smart Devices
The need for Ultra-Secure Mobility™ Products
The demand for the products from Aegis Secure is huge. As highlighted by the Data Bridge Market Research report, the Ultra-Secure Mobility™ market is projected to reach USD 5,967.30 million by 2027 witnessing market growth at a rate of 19.80% in the forecasted period between 2020 to 2027. While once limited government agencies, aerospace and defense – this new and robust demand is being driven by the enterprise market that is now demanding this same level of security. Despite this rise in demand we will, to the best of our efforts, provide the best customer service we can provide.
